creepy/scary/fucked up DARKNETS 0_0
I'm going with story someone made up to post on 4chan and freak people out.
(article isn't really relevant, but anyway).
http://thecolligere.com/internet/intro-to-deep-web
(article isn't really relevant, but anyway).
http://thecolligere.com/internet/intro-to-deep-web
Joined: Sep 2005
Posts: 34,402
Total Cats: 7,523
From: Chicago. (The less-murder part.)
Cracker, phreak, cyberpunk, use whatever nomenclature you find most appropriate. But the title of hacker is a sacred honor bestowed upon the wizardly, not bandied about to describe any punk with a packet sniffer.
Though in fairness, I'll admit to devious use of same myself...
The aforementioned university, at the time when I was there, had begun to install large numbers of general purpose PCs (and small numbers of X-terminals) in many locations, in lieu of the VT-220 dumb terminals. Many of these machines were situated together in a large space seating hundreds of users, which formed the ground floor of the CIRCA building, and from which you could peer through the glass at the two majestic VAX 11/780 mainframes with their RA-81 disk drive cabinets (and the less visually impressive but rather more useful rack containing a cluster of DEC Alpha machines.)
The PCs were mostly of the IBM PS/2 variety, fairly unimpressive. I can't even recall which OSes they all had on them. They could be used for word processing, running NCSA Mosaic (holy ****! The Web with PICTURES! This was heady stuff at the time), sending print jobs to a cluster of dot-matrix printers (these were much slower, obviously, than the big DEC band printers, but were more convenient as they were self-service), etc.
You could also run NetScout.
The university, for whatever reason, had chosen to network all of these PCs using 10base-2 (coaxial) ethernet, rather than 10Base-T. Cost was probably a factor, as ethernet hubs weren't exactly cheap back then. For those not familiar with ethernet technology, we take it for granted these days that our computer is plugged into a switch or router, and that device provides all manner of intelligent traffic switching functions. Not so with 10B2. That was a switchless broadcast network, in which each computer was connected directly to the next in daisy-chain fashion, with a terminator at one end and a connection to some larger network at the other. In practical terms, this meant that every single packet transmitted from any one computer was broadcast to every other computer on the segment, and it was the responsibility of each individual PC to analyze the packet and determine whether or not that packet was intended for it. This is a massively inefficient way of doing things, but it's cheap and simple to implement.
Now, these were the days before we took encryption for granted. Sure, a few truly paranoid folks used PGP, but it wasn't like the connection between your web browser and whatever server you were accessing was in any way secure. For that matter, a lot of folks still used Telnet, Gopher, and Archie / FTP for their day-to-day computing needs. To the designers of those systems, security meant making sure that the door to the room containing the server closed behind you.
It goes without saying that we ended up with a database of the usernames and passwords of a significant fraction of the student body. This was before it was commonplace to transmit things like credit card numbers across the internet so there was no financial gain, so in the grandest tradition of chickenshit nerds everywhere, we mostly used it as a revenge tool against people who we didn't particularly like.
Though in fairness, I'll admit to devious use of same myself...
The aforementioned university, at the time when I was there, had begun to install large numbers of general purpose PCs (and small numbers of X-terminals) in many locations, in lieu of the VT-220 dumb terminals. Many of these machines were situated together in a large space seating hundreds of users, which formed the ground floor of the CIRCA building, and from which you could peer through the glass at the two majestic VAX 11/780 mainframes with their RA-81 disk drive cabinets (and the less visually impressive but rather more useful rack containing a cluster of DEC Alpha machines.)
The PCs were mostly of the IBM PS/2 variety, fairly unimpressive. I can't even recall which OSes they all had on them. They could be used for word processing, running NCSA Mosaic (holy ****! The Web with PICTURES! This was heady stuff at the time), sending print jobs to a cluster of dot-matrix printers (these were much slower, obviously, than the big DEC band printers, but were more convenient as they were self-service), etc.
You could also run NetScout.
The university, for whatever reason, had chosen to network all of these PCs using 10base-2 (coaxial) ethernet, rather than 10Base-T. Cost was probably a factor, as ethernet hubs weren't exactly cheap back then. For those not familiar with ethernet technology, we take it for granted these days that our computer is plugged into a switch or router, and that device provides all manner of intelligent traffic switching functions. Not so with 10B2. That was a switchless broadcast network, in which each computer was connected directly to the next in daisy-chain fashion, with a terminator at one end and a connection to some larger network at the other. In practical terms, this meant that every single packet transmitted from any one computer was broadcast to every other computer on the segment, and it was the responsibility of each individual PC to analyze the packet and determine whether or not that packet was intended for it. This is a massively inefficient way of doing things, but it's cheap and simple to implement.
Now, these were the days before we took encryption for granted. Sure, a few truly paranoid folks used PGP, but it wasn't like the connection between your web browser and whatever server you were accessing was in any way secure. For that matter, a lot of folks still used Telnet, Gopher, and Archie / FTP for their day-to-day computing needs. To the designers of those systems, security meant making sure that the door to the room containing the server closed behind you.
It goes without saying that we ended up with a database of the usernames and passwords of a significant fraction of the student body. This was before it was commonplace to transmit things like credit card numbers across the internet so there was no financial gain, so in the grandest tradition of chickenshit nerds everywhere, we mostly used it as a revenge tool against people who we didn't particularly like.
EDIT: My work computer:
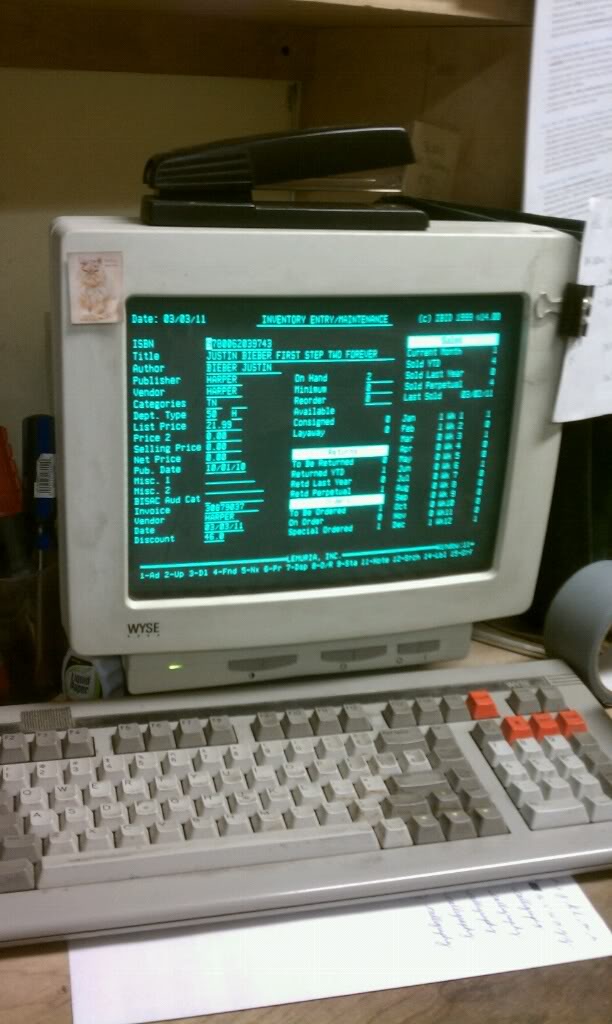
Last edited by mgeoffriau; Mar 3, 2011 at 03:02 PM.
Yes that's why I didnt comment on the filesystem size. There were probably middleware apps that would allow a network mount or even volume managers
Btw joes anecdote is how the real deal would sound... Full of lots of **** the layperson would not understand.
Fwiw I had a ps2 joe it was my familys first computer. My mother did get on the web too in 94 and was jabbering about mosaic and usenet back then. She wasa professor at the time. I wonder what nascent tech is propagating in academia nowdays? Prob nothin as awesome as the web
Darknet is anything that's not indexed by search engines, right? So FTP, newsgroups, etc are all darknet as well I believe.
But there is alot of screwed up stuff on there that can be accessed through TOR. I believe you have to disable Java and some other things in your browse since many of those sites are monitored by the FBI (especially the pedo sites). I personally wouldn't mess with it. There was a super long thread on body building forum about this a while back.
But there is alot of screwed up stuff on there that can be accessed through TOR. I believe you have to disable Java and some other things in your browse since many of those sites are monitored by the FBI (especially the pedo sites). I personally wouldn't mess with it. There was a super long thread on body building forum about this a while back.
Joined: Sep 2005
Posts: 34,402
Total Cats: 7,523
From: Chicago. (The less-murder part.)
I wonder what nascent tech is propagating in academia nowdays?
Darknet is anything that's not indexed by search engines, right? So FTP, newsgroups, etc are all darknet as well I believe.
But there is alot of screwed up stuff on there that can be accessed through TOR. I believe you have to disable Java and some other things in your browse since many of those sites are monitored by the FBI (especially the pedo sites). I personally wouldn't mess with it. There was a super long thread on body building forum about this a while back.
But there is alot of screwed up stuff on there that can be accessed through TOR. I believe you have to disable Java and some other things in your browse since many of those sites are monitored by the FBI (especially the pedo sites). I personally wouldn't mess with it. There was a super long thread on body building forum about this a while back.
WTF is TOR???
Think of tor as a proxy on steroids. It wont do what kenzo was talking about, but what it does allow you to do is surf the internet/download/P2P with almost complete anonymity.
Instead of directly connecting to a website/server, you send network traffic through a tunnel (tor) which then comes out randomly at another location and connects to the destination. The destination server then sends its reply back through the tor tunnel to your PC.
Heres the catch: say you connect to amazon.com through tor. You are in the US, but the outlet for the tor network might be in Moscow. Then you disconnect and come back the next day. This time it might be in Beijing. This is what creates the anonymity, you will (in theory) never connect through the same path twice.
The downside to this is that it is very slow.
Instead of directly connecting to a website/server, you send network traffic through a tunnel (tor) which then comes out randomly at another location and connects to the destination. The destination server then sends its reply back through the tor tunnel to your PC.
Heres the catch: say you connect to amazon.com through tor. You are in the US, but the outlet for the tor network might be in Moscow. Then you disconnect and come back the next day. This time it might be in Beijing. This is what creates the anonymity, you will (in theory) never connect through the same path twice.
The downside to this is that it is very slow.
https://www.torproject.org/
Never heard of this before! I torrent a lot and this looks great. Hmm